Official Write-Up for the Lucky Panther CTF
Lucky Panther CTF TryHackMe Room
You can also join this room by going to My Rooms page and entering Code: luckypantherctf
Task 1: Download the Image
Start by downloading the provided image file.
Task 2: Investigate the Image
Question 1: What Did You Find in the Picture?
To get started, you can try using online tools. Such as: aperisolve , stegano … . But I’ll skip this part and move on to the terminal.
Just now let’s try commands:
1
2
3
4
file
strings
exiv2 <file.name>
binwalk -e <file.name>
And now closer to the point, use the steghide tool to analyze the image:
1
steghide info luckypanther.jpg
Output:
1
2
3
4
5
"luckypanther.jpg":
format: jpeg
capacity: 28.7 KB
Try to get information about embedded data? (y/n) y
Enter passphrase:
Since a passphrase is required, we need to find it. Let’s try StegSeek with the rockyou.txt wordlist:
1
stegseek luckypanther.jpg /usr/share/wordlists/rockyou.txt -
StegSeek successfully finds the passphrase:
1
2
StegSeek 0.6
[i] Found passphrase: "$pinkpanther"
Next, extract the hidden file using steghide:
1
steghide extract -sf luckypanther.jpg
Enter the passphrase "$pinkpanther" to extract the embedded file, which is forest.zip.
Answer: forest.zip
Question 2: What is Your Second Find?
Let’s unzip the forest.zip file:
1
unzip forest.zip
Output:
1
2
Archive: forest.zip
forest.zip: deepforest.pdf password:
The forest.zip file is password-protected. To crack it, use fcrackzip:
1
fcrackzip -u -D -p /usr/share/wordlists/rockyou.txt forest.zip
After running the command, we find the password:
1
PASSWORD FOUND!!!!: pw == deepforest
Unzipping with the password deepforest reveals the deepforest.pdf file.
Answer: deepforest.pdf
Question 3: What is Hiding in the Deep Forest?
Opening deepforest.pdf requires a password. To crack it, first extract the hash using pdf2john:
1
/usr/share/john/pdf2john.pl deepforest.pdf > deepforesthash
Then, use John the Ripper to crack the hash:
1
john --format=PDF --wordlist=/usr/share/wordlists/rockyou.txt deepforesthash
John successfully cracks the password:
1
good-luck (deepforest.pdf)
Alternatively, you can use Hashcat. First, edit the hash file by removing deepforest.pdf: from the start, and save it as deepforesthash2.
To crack the hash with Hashcat:
1
hashcat -m 10500 deepforesthash2 -a 0 /usr/share/wordlists/rockyou.txt
Hashcat confirms the password is good-luck.
Now, open deepforest.pdf with the password good-luck to reveal the first flag.
Answer: GUZ{U!_U4px3e!_l0h_4e3_va_4ur_Q33c_s0e3$g!_P0ate4g$!}
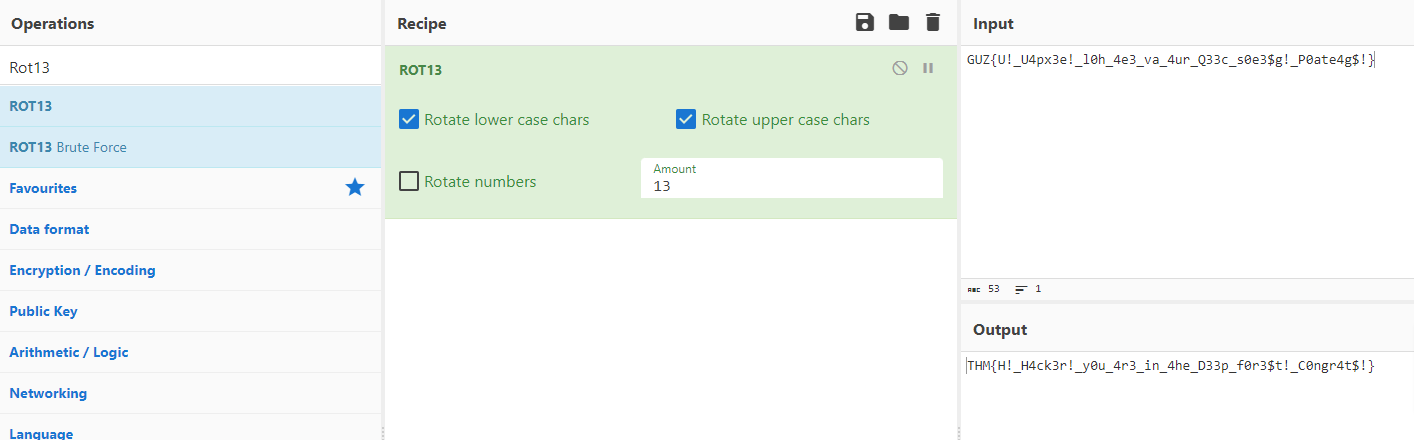
Task 3: What is the Flag?
Just a little more deciphering left.
Are you in the Deep Forest?
Question: What is the Flag?
We have a flag example from Task 2:
1
GUZ{U!_U4px3e!_l0h_4e3_va_4ur_Q33c_s0e3$g!_P0ate4g$!}
Using the Cipher Identifier tool at dCode, we identify it as a ROT13 cipher.
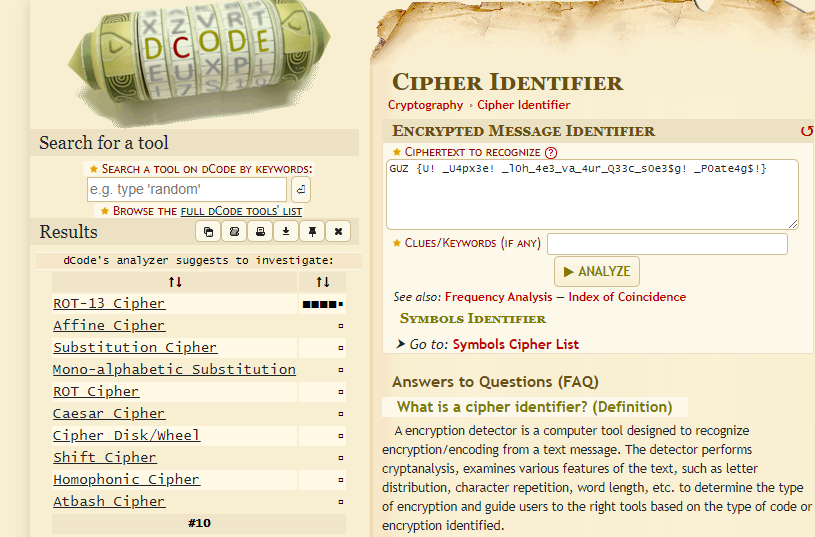
click on ROT-13 Cipher and decrypt srting:
We can decode it directly using ROT13, or by using CyberChef with the ROT13 function.
Answer: THM{H!_H4ck3r!_y0u_4r3_in_4he_D33p_f0r3$t!_C0ngr4t$!}
Great! Happy Hacking!